Okay, so check this out—wallets changed. Fast. Wow!
At first glance a browser extension that holds crypto looks small and harmless. Really? Not always. My instinct said “trust the app store”, but then I kept finding shady clones and weird permission requests. Hmm… something felt off about a handful of extensions that looked identical to legit ones. Initially I thought that a popular name alone was enough. Actually, wait—let me rephrase that: popularity is necessary but not sufficient.
Here’s the thing. A DeFi wallet browser extension for Solana isn’t just a convenience. It’s the gatekeeper to tokens, NFTs, staking, and on-chain identity. Short keys live on your device, and that means a browser extension must get two things right: secure key handling and sane, minimal permissions. On the other hand, usability matters too—if the flow is clunky, people will copy/paste bad seeds into chat windows (sadly common). I’m biased, but user experience can be a security feature.
So let me walk through what I look for when choosing a Solana extension—and why some choices make me nervous. On one hand you want quick trades and integrated dApp support. Though actually, too much automation can be dangerous if the extension auto-approves things without clear UX. There’s a balance. Also, small tangents here: browser variability matters (Chrome vs. Brave vs. Edge) and platform quirks can leak into the user experience—especially on Windows where background processes behave oddly sometimes…
Picking a solid Solana wallet extension — practical markers
Start with provenance. Check who built it. Check GitHub. Check whether security audits are public. Seriously? Yes. Look for multisource verification rather than trusting screenshots or marketing blurbs. If you want a quick pick to try, consider the officially recognized options, and read user reviews and changelogs. A good place to find an official download link is this phantom wallet page: phantom wallet. But don’t stop there—verify the extension ID in the browser store and confirm signatures where available.
Short checklist—quick and ugly: secure seed storage; no overbroad permissions; frequent updates; public audits; clear transaction signing UI. Wow, that list looks like common sense, and yet it’s not followed often enough. Somethin’ I always do: create a small test wallet first and send one tiny transaction to validate the flow before moving any serious funds. Seriously, testnet or a dust transfer helps.
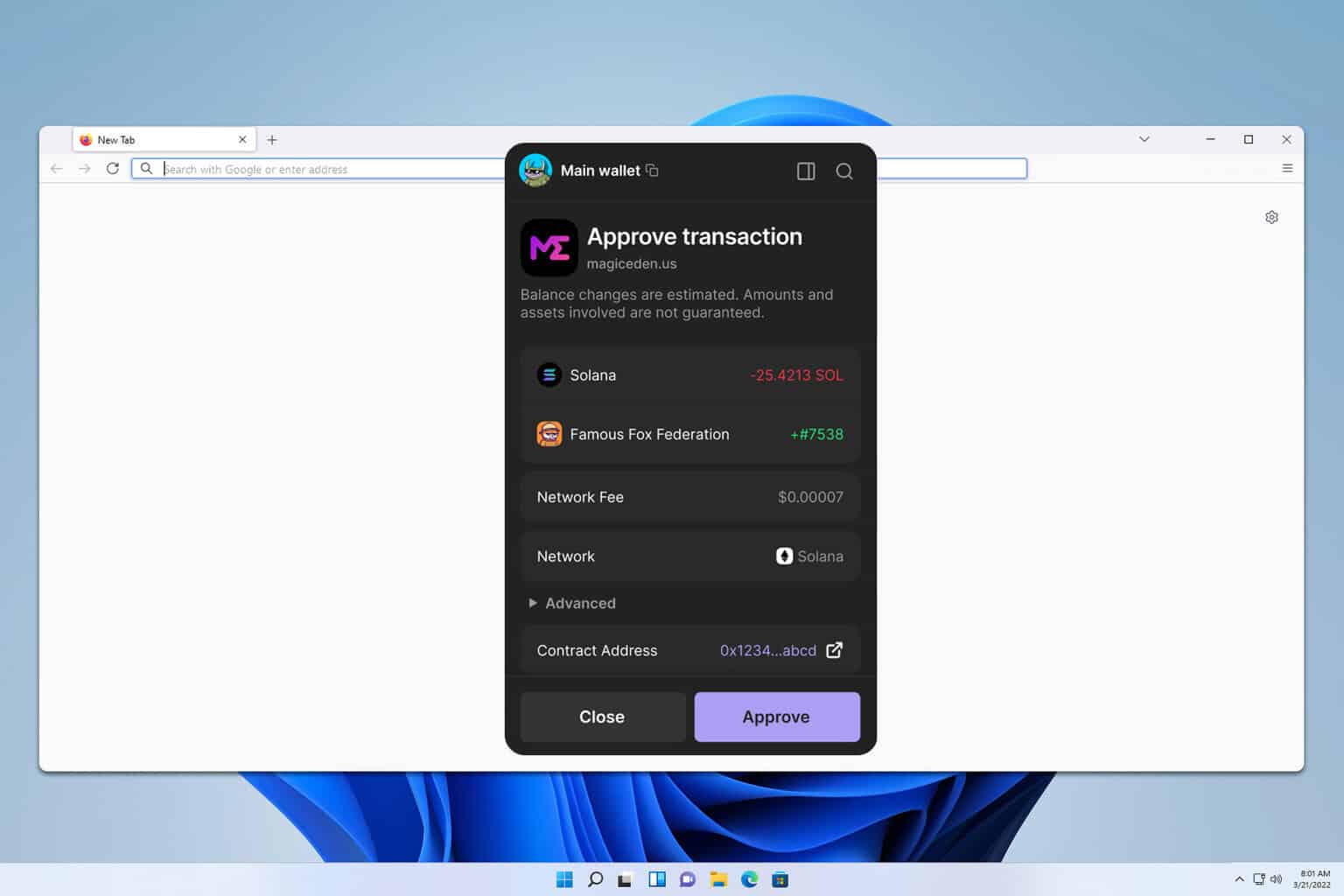
Another practical marker: how the extension presents transactions. If the UI shows only “Approve” with no token, amount, or destination details—leave. Immediately. That’s a red flag. On the flip side, extensions that show raw instruction details and allow granular rejections are doing the right thing, though it can be intimidating for new users. I’m not 100% sure every user wants that level of detail, but I prefer explicitness over mystery.
Now—security trade-offs. Extensions need permission to interact with pages, but some ask for blanket read/write access to all sites. On one hand that enables wide dApp support. On the other, it increases attack surface. For me, minimal request scopes are preferable. Initially I thought “just enable everything for convenience”, but after a couple near-miss phishing attempts, I changed my view. Actually, I changed it hard: less is better.
Permissions and browser security aside, backup hygiene matters. If your recovery phrase is exported to plain text or sent over networks, that’s game over. Use offline backups, hardware wallets, or dedicated password managers that support secret notes. If you connect a hardware wallet to the extension, that raises your security baseline—though it also adds complexity. I’m biased toward hardware-backed keys when significant funds are involved.
Usability quirks are worth calling out. Some extensions timestamp transactions oddly. Others group multiple instructions into one ambiguous approval screen. That part bugs me. Also, mobile integrations vary: some extensions pair neatly with mobile apps; others are orphaned. If you plan to use mobile dApps often, test the mobile handshake workflow first (or you’ll be annoyed later).
Let’s talk audits and community. A clean audit from a reputable firm is helpful, but it’s not a magic stamp. Look for active issue trackers and community engagement. Are bugs being fixed? Are maintainers responsive? On the other hand, a huge user base with poor support could be worse than a smaller, well-maintained project. On balance, active maintainers and transparent changelogs matter a lot to me.
Final note on scams and clones: phishing tactics have evolved. Malicious pages now mimic wallet popups and even fake extension pages in the store. My gut flips when a site offers “instant verification” or “official-looking download buttons” outside of browser stores. If something looks rushed—like a cheap landing page or odd domain names—step back. Take a breath. Verify via multiple channels: official social accounts, reputable forums, GitHub repos. And if you’re unsure, ask. The community is usually quick to warn about scam pages.
FAQ
How do I confirm the extension is legitimate?
Check the developer name in the browser store, verify the extension ID (if published by the team), look for GitHub repos and audit reports, and test with a small transaction. Oh, and compare the extension listing with the project’s official site or social channels—if those disagree, don’t install.
Should I ever store large amounts in a browser extension?
Short answer: cautious yes. Use a hardware wallet for large holdings where possible. If you must keep funds in an extension, use strong OS security, a dedicated device, and never reuse the recovery phrase elsewhere. Also, keep software updated and avoid unnecessary permissions.
Is the official store enough to trust an extension?
Being in the Chrome Web Store or other storefront is necessary but not sufficient. Stores can be abused. Cross-check the publisher, read recent reviews, and confirm via the project’s official channels. If anything feels off, pause and investigate.
Leave a Reply